
For years, I've been a fan of the internet filtering software Net Nanny. I'll explain why in a moment.
However I've just had to uninstall it, and I'm now looking for an alternative. (If you, personally, use something similar, please comment below with any recommendations of products to try or to avoid).
The problem relates to browsing certain sites that use SSL / TLS / https. I'll also, shortly, explain how that problem presents itself. The real purpose of this post is to explain exactly what the problem is and why it occurs. Searching the web for the error messages led me nowhere, and Net Nanny's technical support initially gave me conflicting explanations and advice. Only when I explained the problem to them did they say that this is a known issue. Why they didn't tell me that earlier, I'll never know. I'm hoping that writing up this review will help others who have found the same problem, but who have not found any explanation or solution.
I've had this problem with their software for about a year, but two changes in the internet (again - I'll get there) have meant that these problems are now presenting themselves more frequently. It's reached the point where the product is, sadly, unusable. TL;DR — use something else until they fix this.
Net Nanny — a great parental controls suite
The internet is a great place. It's also a place with dark corners, where dangers lurk. This presents a dilemma for the modern-day parent. We want our children to explore and become proficient in using the internet; we want to protect them from things that are scary, profane, violent, and abusive. If only we could set up their web browser so they could explore the safe areas of the internet happily, whilst being blocked from going onto the nastier areas of it.
Well, NetNanny is just such a piece of software. You can set it up very quickly if you wish. After installing, create an account for each member of the household that will use it. Give it the age of each person, and it will automatically set it up to block the most appropriate categories for them. If Net Nanny is installed on a computer, every user needs to have a Net Nanny account, because all internet traffic is screened. Any adults who don't wish to have filtering (although, given the software is running, may I suggest there are some categories you may wish to block yourself from?) can simply have an account that lets everything through.
If you wish, you can set things up with far more granular control:
- Each webpage is assigned one of about 30 categories by Net Nanny. For each account, you can decide which categories you'll allow through.
- In fact, for any category, as well as "allow" and "block" there's also a category of "warn", which means the end-user sees a warning but can click past it if they wish.
- You can choose to mask swear words within a webpage rather than blocking the entire page.
- You can whitelist particular sites for the whole family, but you can also assign individual domains to any of the given categories yourself. You can create custom categories (for example, I set one up for "video" sites, into which went things like YouTube and Vimeo), and then choose to block or allow them for individual family members.
- You can also control which hours of the day to allow web access for each person.
- If an end-user feels that a page has been incorrectly blocked, they can complete a simple form, which sends an email to the administrator to say so.
It is an extremely powerful suite. By and large, it simply works, even using the quick, out of the box, settings. Which is why it was a shame to hit these new problems.
What the problem is
With some websites that use https / SSL, you see an error when browsing with a computer that has Net Nanny installed. Note that the problem arises when Net Nanny is installed. If your user account is set to allow every website, you'll still get the error.
The error takes the form of a warning that the browser session is not secure.
Your connection is not private. Attackers might be trying to steal your information from www.example.com (for example, passwords, messages, or credit cards). ET::ERR_CERT_WEAK_SIGNATURE_ALGORITHM
Chrome gives you a "read more" link, but it doesn't shed much light on why you're having this problem. It doesn't point to the fact that Net Nanny is the culprit; in fact it suggests that the website may have their SSL incorrectly set up. You're being warned for your own protection.
You can get past the warning by clicking "Advanced" in Chrome, and telling Chrome to go to the webpage anyway. That's a bad idea for two reasons:
- It develops a mindset that security warnings are there to be ignored. They're not. Usually, a warning like that means exactly what it says. If you continue, your traffic is not securely encrypted. Don't train yourself to click past warnings like that. If you see that when you're browsing a website, your response should be to get out of there.
- It fails to distinguish what the problem is. If the problem is solely with Net Nanny's filtering, you would be OK to click past provided it doesn't become a reflex. If the problem was with the website, you would not be OK to click past. The warning doesn't tell you which is which. If you learn to click past warnings on a computer using Net Nanny, the day may come when you click past a warning that was actually about the website and not just about Net Nanny. Cue: The Boy who Cried Wolf.
The problem is actually more subtle. Sometimes, the main domain of the website is fine, but they use a different (sub-) domain for some other content which does get blocked. In this case, the secondary (sub-)domain gets blocked silently, and there's no "Advanced" link to click you past the problem:
- This may affect resources like images, CSS files (which control how a webpage appears) and JavaScript (which makes login and "add to cart" buttons work). This makes the whole webpage look wrong. Think: Everything in Times New Roman, just laid out black text on a white background, each item below the one above in an identical font size, and no buttons or links work.
- Remembering that Net Nanny is mainly about keeping children safe, some games websites use different (sub-)domains for the flash files that power games. The web page that loads fine, but the flash game silently doesn't work.
- Other times, it's more annoying if you're trying to work. Most lately, we found that Office 365 online email loaded the list of messages, but the AJAX command to open a message when you click on its subject didn't work. It turns out this relied on some javascript in a blocked resource.
There are ways to work around these more subtle annoyances. But they're 5 or 10 clicks to do, and require some knowledge of the source code for a webpage and how to use Chrome Developer Tools. Even if you wanted to train your 4 year old to skip past browser security warnings, we're now beyond the technical abilities of a 4 year old.
So why are these warnings appearing? Well, it's all to do with how SSL works:
How SSL works, and why it makes filtering tricky
This is an extremely simplified explanation of what happens when you browse a webpage with the https protocol. Fuller explanations are available online if you're interested; I'll explain enough to explain the problem.
When you browser a normal webpage, that starts "http://", all the traffic between your browser and the web server is en clair, unencrypted, plain text. Web traffic needs routing, which means it passes through about 10 intermediate servers / routers on its way. At any point, conceivably, someone could have installed software to inspect the content of the traffic. What is sent to your browser could be read, and data you send to the server could be read. Most concerningly, the session cookies that authenticate you as a logged in user could be sniffed out, which would then allow someone else to browse that website using your login.
For this reason, where security matters, you want to have that traffic encrypted, so that only you and the web server can understand it. To do this, you use a website with "https://" instead. Here (remember, over-simplified) is what happens:
The web server sends your computer it's SSL certificate. This contains a key that will allow you and the web server to communicate in private.
The important thing is that the certificate is also signed. This is another piece of encrypted data that confirms who issued the certificate. Why do you need to know the issuer? Well:…
I could set up a fake server that claims to run Facebook. I'm hoping to trick your computer to visit my server instead of a real Facebook one, that you'll log in, and so I can steal your password. To do that, I could create myself a certificate to let you browse facebook.com. But I'd have to sign it myself. Your web browser won't trust my certificate, because it's not signed by someone trustworthy.
But what about the real facebook.com? How does your web browser know to trust its certificates? They get those certificates signed by a company who is trustworthy and who has verified that the request comes from the real Facebook. Their certificate is, maybe, signed by someone else. But sooner rather than later, you end up with one signed by a "root" certificate — one of only a small number of universally trusted certificates. Your operating system (Windows, MacOS, Linux, Android) comes with a preinstalled list of trusted "root certificates". Anything that can be traced back to these is OK.
SSL creates a challenge for filtering software like Net Nanny. Net Nanny sits between your operating system and the big wide internet. It is one of those packet sniffing tools that I just mentioned. Only this one is not malicious. It's on your computer, not some third party router, and it's there to perform a filtering function you want it to do. That's all fine for good ol' http:// websites. But https:// websites are encrypted by your web browser, and only the web server has the key to decrypt that traffic. Net Nanny will not be able to read any of your https:// traffic, which means it won't be able to filter it.
How Net Nanny filters SSL traffic
How does Net Nanny get round this problem?
The answer is, it installs itself as a proxy between you and the webserver. It runs a little process in the background on your computer, a bit like a mini web server. If your computer needs to access a website, it doesn't go to the website. It asks the Net Nanny proxy, which then asks the webserver, before passing the answer back.
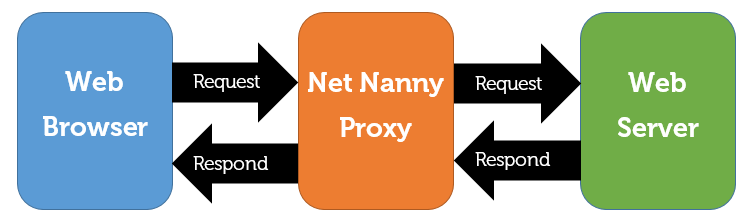
This is technically called a "man in the middle". Usually, you want to avoid these. You want your encryption to be end-to-end. Only in this case, once again, you do want this. It's not some third party MITM attack; it's a piece of software you've installed to do some filtering. With SSL websites, however, Net Nanny can't simply sniff the packets of data passing between you and the internet. It actually has to decrypt them.
So, your browser makes a request, which it encrypts with (what it thinks is) the encryption key for the website your visiting. The Net Nanny proxy decrypts that request, and then encrypts it with (what really is) the encryption key for the website. The website then encrypts the response and sends it back to Net Nanny, which is able to decrypt it. Finally, having filtered, it re-encrypts the response to send it back to your browser.
The conversation between Net Nanny's proxy and the web server is easy. Net Nanny simply has to act like any other web browser on a computer that doesn't have filtering software. It requests the SSL certificate for the web server, checks that it's signed by someone trustworthy, and then uses the key it's been passed to encrypt the request, and finally uses that same key to decrypt the result.
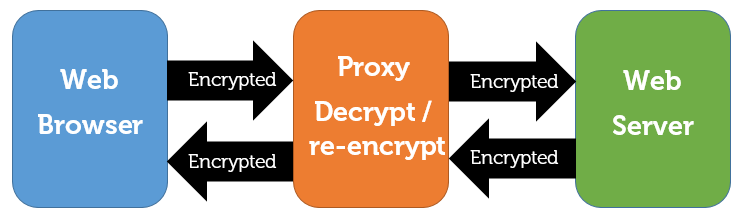
The tricky bit is the traffic between the web browser and the Net Nanny proxy. And here is where things go wrong.
Traffic between the Web Browser and Net Nanny's proxy
The Net Nanny proxy has to give your browser an SSL certificate for the domain you're trying to browse. This certificate has to contain a public key that can be used to start the encrypted conversation. But it has to be a public key for which the Net Nanny proxy holds the private key, otherwise the proxy cannot hold that conversation. Only the website's server holds the private key that corresponds to the public key in their actual SSL certificate. It's called a private key for a reason. So Net Nanny cannot use the website's actual SSL certificate.
This means they have to create their own, and get it signed. If you've followed me thus far, you'll know this also presents a problem. No trusted certificate signer is going to sign their home-made certificate for, say, facebook.com. So they're going to have to sign their own certificate.
Again, if you've followed me, you'll anticipate the next problem. If they've self-signed their certificate, your browser won't trust it. … Unless you tell it to.
Remember your computer has a store of trusted root certificates? Each user profile in Chrome or Firefox also has a list of trusted root certificates. When you install Net Nanny, it adds their own certificate to the trusted certificates store for your web browser. That's the magic step that makes it all work. (Or not.) You can find the certificate they use at C:\Program Files\ContentWatch\ContentWatch Trusted Root Authority.pem. Sometimes, things go wrong, and Net Nanny Support get you to reinstall that certificate.
Why You get Browser Warnings
So what goes wrong?
There's one more concept to introduce, that of a cipher. To encrypt / decrypt data, you need two things: a cipher, and a pair of keys.
Think of the cipher as the machine that turns the en clair text into encrypted text, and back again. Think of the key as something you plug into the machine when you encrypt, so that the message can only be decrypted when the other key is in the machine. Some key pairs are symmetric (the same key is used to encrypt and decrypt), others are asymmetric (you need a public and a private key that match). Regardless, you need the cipher to do the actual work.
Not all ciphers are equally secure. Picture a fictitious cipher that only uses the first numeric digit in the key when it encrypts data. There would only be 10 truly different keys, and any computer could decrypt anything in at most ten attempts.
When a browser first starts a conversation with a web server about a possible https session, they discuss what ciphers might be used. They will try to find the most secure cipher that both browser and server can understand.
For certain websites (and I've never worked out why it's only some), the Net Nanny proxy (acting as the fake web server) only offers a certificate that has been signed using the encryption cipher SHA-1.
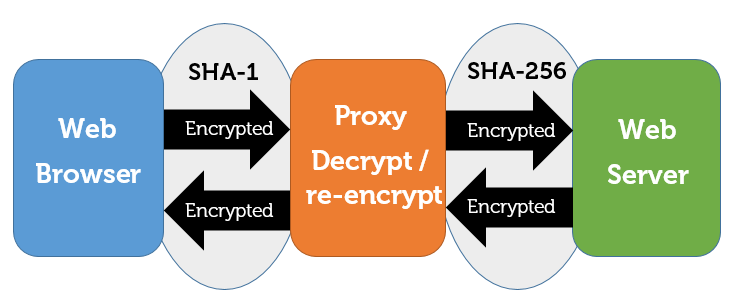
This cipher was OK back in the day. But now that computers have become more powerful, and now that weaknesses have been found in the SHA-1 algorithm, SHA-1 encryption can be cracked. In other words, if the certificate is signed using SHA-1, it's possible that someone malicious has faked the certificate's signature. So Chrome and Firefox, correctly, warn you that traffic using an SHA-1 certificate is insecure.
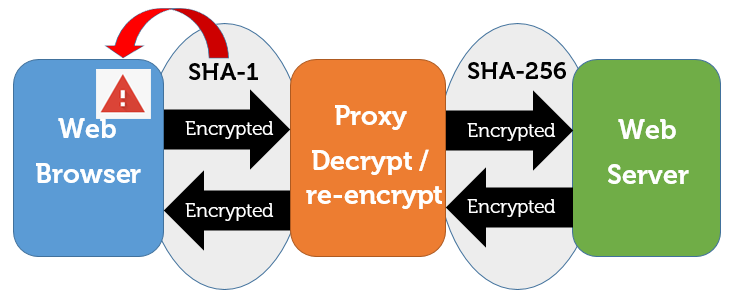
Sure enough, if you look in Chrome Developer Tools at the certificate that is triggering the warning, you'll see that it was issued by ContentWatch (the parent company for Net Nanny), and uses SHA-1 encryption.
Where exactly does the problem lie?
So, the problem lies within the Net Nanny proxy (and not with the website you're visiting). For some websites, it generates a certificate to allow it to communicate with your web browser. The certificate is signed by a "root" certificate that your computer has been told (by Net Nanny) that it can trust. But the certificate it presents is only an SHA-1 certificate. So a modern browser rejects it with the "certificate error" warning you get.
How can they solve it?
I don't know the details of how Net Nanny works, so I can't give a detailed solution. They need to issue SHA-256 certificates for every website for which they act as a proxy. They already do this for some websites, and I do not know enough about how it works to see why they cannot do it for all.
Why is this problem becoming more apparent now?
There are two recent developments that have made this problem a more frequent one.
First is the increased take-up of SSL. There is a move afoot, supported by Mozilla and Google, to get "https everywhere". Google have indicated that they will rank sites more highly in search results if the website uses https. I believe it has now reached the point where over 50% of web traffic takes place over https.
More SSL websites means more sites that present this problem. Go back two years, when only shopping-type websites really bothered with SSL, and the kinds of websites that most children would use never encountered this.
Second is the vulnerability of SHA-1. The flaw that makes SHA-1 insecure was only discovered in a way that is easily reproduced in February 2017. That led to website owners re-issuing their certificates not to use SHA-1. Browser developers gave a reasonable amount of time for website owners to do this, before releasing new versions that blocked sites using SHA-1 certificates.
So now we have the perfect storm: Lots of sites using SSL (which means more sites using SSL via an SHA-1 certificate through Net Nanny), and browsers actively rejecting those SHA-1 certificates.
Net Nanny is Content Watch's flagship product. But until this is fixed, it's unusable with the modern internet.
Recommendations?
Over to you. What parental controls / filtering software have you found to work well? Does it work with, and filter, all https sites? Are there any that you've tried and would advise me to steer clear of?
Please use the comments below to make your suggestions.
Guide for Firefox
Here is a guide I found to make it work in Firefox:
https://geekvisit.com/trouble-accessing-https-sites-firefox-sec_error_c…
Not a perfect solution since you then will be trusting a somewhat insecure certificate if I understand your explanation well enough after just having skimmed through it, but it is good enough for me since I don't want to switch from netnanny.
Sadly, not quite
Thanks for that link
Sadly, it doesn't solve it. That page describes how to import, manually, Net Nanny's root certificate into the trusted certificate store for Firefox. That is something that the Net Nanny installer already does, but sometimes it gets removed and those steps need following. I actually mentioned that in my main post:
Remember your computer has a store of trusted root certificates? Each user profile in Chrome or Firefox also has a list of trusted root certificates. When you install Net Nanny, it adds their own certificate to the trusted certificates store for your web browser. That's the magic step that makes it all work. (Or not.) You can find the certificate they use at C:\Program Files\ContentWatch\ContentWatch Trusted Root Authority.pem. Sometimes, things go wrong, and Net Nanny Support get you to reinstall that certificate.
If that alone solves your problem, then great! It didn't for me, because the problem was not the certificate but the cipher used by the proxy to re-encrypt the SSL traffic as it is passed to the browser.
User Settings Allow Toggling Off
I'm considering Net Nanny with a two week trial and found the same problem. But when I went into my user settings, I discovered that there's an option to toggle off "Filter secure content (SSL/TLS)." It's under "Additional Settings."
Yes, but
Yes, if you choose that option (i.e., if you chose to turn off "filter secure content"), the problem goes away. The reason it goes away is that it stops filtering https traffic, and only http (non-secured) pageviews get filtered. That means any child of any age could visit any site that was https, without NetNanny applying any of its filtering rules (including domain blacklists).
That was always risky. It's now very risky, because there's a push to have all websites use https. Chrome's next release, in a few weeks time, will mark as "insecure" sites that still use http. So if you "solve" the problem by turning off https filtering, you'll soon be bypassing the filtering system for the vast majority of traffic.
Thanks for quick answer
Hi James,
Well, that definitely sounds crazy, if I'm reading you right. If I install NN, and then toggle off the 'filter secure content' that means essentially that the very reason why I installed NN is undone? Is it really the same as simply uninstalling the program? I'm going to also contact NN and see what the deal is with this, and I'll report back here what I find.
We used Covenant Eyes for years, but it caused me, the primary user of the computer, no end of trouble. I work online and CE would randomly and frequently block sites that made no sense to block, like my Blackboard accounts. I also had to wait forever when turning on my computer for it to start up, crash, and start up again. Regular calls to CE and reinstalling new versions didn't seem to help. But in fairness, this problem doesn't show up on our other Windows 10 computers (laptops), so that's still a mystery. With CE, if I need to, you know, WORK, I had to go through the process of uninstalling and restarting and then remembering to install again. With NN, I have the option to disable, which I love. I am REALLY hoping that NN can work for me, so I'll pursue this and get back to you if I discover anything.
Thanks, by the way, for taking the time to write such a helpful and well-written page.
Keep in touch
Yes, it's crazy. The history of this with NN was:
- Offer filtering only of http pages. https can't be filtered, because NN can't analyse traffic that's encrypted
- NN invents a way to get round this, by having NN itself decrypt the webpages as they come through, analyse them, and if they're allowed re-encrypt before passing to the computer. (This is done by having NN install its own root certificate, as I've documented in this post)
- Security analysts discover flaws in some of the earlier cryptographic algorithms. These are fixed, and the fix relies on websites only to allow the newer, safe, methods of encrypting.
- Eventually, browser developers block the insecure ones. The problem is that, for some reason, NN re-encrypts with insecure cyphers on some websites. Those browsers that block those insecure cyphers therefore block NN-filtered traffic from those sites.
And that's where we're stuck. I opened my first ticket with NN about this well over a year ago. With the incresaing take-up of https for all sites, NN was becoming unusable. so I disabled it in February, then never renewed it in April. A fresh ticket got them, finally, to admit the problem, but they never solved it. From what you're saying, they still haven't. This is a critical flaw at the core of their core product, so I don't know why they haven't pushed this to the top of the pile.
Anyway: I'm glad you found my post helpful! :-). Keep in touch if / when you get anywhere with their support people.
Yep. Just Like You Said
I talked with Net Nanny Tech Support, trying my best to sound like I knew what I was talking about so we could hop over the "Did you try uninstalling and reinstalling?" phase. I was told that the problem was a conflict between my antivirus and Net Nanny, and if I turned off the web shield of the antivirus, all would be well. I knew this wasn't the case (both because of your tutelage above and my own former troubles with CE when I was also told that a similar problem was the antivirus). I asked him if, when I toggled off the "Filter secure content," I would still get reports of bad places visited, and he said No. Just to confirm, I asked him if toggling that off were the same functional thing as either diabling or uninstalling the program, and he said, "Yes." This is odd to me, since in Net Nanny's Questions Portal, they encourage people to toggle that off if they run into the sorts of trouble we've been running into, without ANY warning of the repercussions.
Anyway, I disabled the antivirus like he said, rebooted the computer for good measure, and you'll never guess... (cue sarcasm): it didn't make any difference. I still couldn't get on my work site, or that den of danger, National Public Radio.
Back to the drawing board. For my purposes, accountability is more important than filtering, since this is primarily being used for adults who want help and oversight with their temptations, rather than children who might stumble somewhere unknowingly.
Finally some answers
Thank you for taking the time to explain these issues with Net Nanny. I have useed the software for years but it is now practically useless. I did contact tech suppport and they told me that they were aware of the issue:
"We were able to replicate the issue on our end with the same site. We apologize for the issue you have experienced. I have had our support group look into this and they are not able to determine what is causing the issue. In order to find out we would need the help of our development team, but unfortunately they are working on an extremely high priority project and I will not be able to have any one look into this for some time.
[When replying to this message, please include all previous correspondence with us. This will help us to serve you better. Thank you.]
M... U...
Customer Service Team Lead"
I woud appreciate updates on this or alternatives.
Mac Pro High Sierra Chrome
Ditto
Yep - that bottom line was the same one I reached with them once they finally admitted the problem. That was 5 months ago. I simply replied to point out that the project really did need to be a high priority, to take precedence over something that was increasingly going to render their flagship product useless. Meanwhile, the proportion of sites using https continues to rise, and their developers are still working on a higher priority matter.
Hopefully someone will post here once there is progress to report.
A shame really. I'd be
A shame really. I'd be curious what this higher priority project is. Better be worth the loss of flagship customers by the time they finish.
Mobicip?
Has anyone had any experience with Mobicip? I've run into the Net Nanny issue after upgrading to High Sierra, and I'm wondering if Mobicip would be a good replacement. I looked at Covenant Eyes, and it doesn't block porn sites, it just monitors and reports internet activity to an accountability partner that you choose. My kiddos are young enough that I don't want them stumbling onto something they can't unsee.
New for me
Thanks - that's a new one for me. If you try it out, please come back here and let us all know how you get on. Or if someone else reading this has used it, please add your comments.
Same here
After reading your article, I reached out to Net Nanny support for myself. After going back and forth several times troubleshooting the issue, I was finally told this:
The issue may be related to the Chrome certificate stores and that we do work well with that sites certificate in Chrome. Unfortunately we do not have a workaround that you can apply to get it to work without compromising the Net Nanny filter.
[When replying to this message, please include all previous correspondence with us. This will help us to serve you better. Thank you.]
Maata Urayanza
Customer Service Team Lead
Technical Support: 1.800.485.4008 | 801.508.3596
P: 801.508.3505
So there's an issue. I finally had to uninstall Net Nanny so most https sites would work. I got an error on some sites and no css on others. Looking at the code, these sites were pulling their CSS from another domain and it was getting the error causing no style sheets to load.
Did you ever find a good, working alternative to Net Nanny?
~Jeremy
Firefox?
Hi Jeremy
Frustrating isn't it? No, I never did find another alternative that works as well as Net Nanny used to before the majority of sites started using SSL.
The ticket reply you pasted raises an interesting question: I don't think I ever checked if the problem I had was specific to Chrome. Easy enough to check - fire up the same site in Firefox or Edge and see what happens. I no longer have any computers with Net Nanny installed to check that, but if someone else wants to test please report back here. Moving to a different browser would be a (not ideal but) perfectly workable way to get filtering working again.
I use Firefox 99.99% of the
I use Firefox 99.99% of the time. I only use Chrome for Google Drive which has worked fine. This could explain why sites in general have worked for me.
I ran into similar error messages with Net Nanny 3
I really hope NN does something about this. I bought NN (Mac) for its content filtering ability, to curb my porn usage. I was using K9 Web Protection before but it's ineffective against youtube and facebook.
Have you had issues with NN when viewing facebook after ignoring the error message? It seriously jacked up how Facebook looks.
If you are interested in porn blocking for IOS, I use IOS's "Limit Adult Content" option and installed Jonathon Arnold's xBlock. xBlock filters Safari traffic via a content filter plugin. Any sites that should be blocked can be sent to the author, who responds within 24 hours.
Update and steps for applying Geekvisit solution to a Mac
I used the helpful SSL certificate importation guide posted by a fellow commenter:
https://geekvisit.com/trouble-accessing-https-sites-firefox-sec_error_cert_signature_algorithm_disabled-sec_error_unknown_issuer-firefox-netnanny-issues/
Did the trick! Firefox now visits SSL sites without that SSL certificate error. Chrome it turns out never had the problem, because Net Nanny already gave it the certificate. Not clear why the Net Nanny installation this morning failed to do so with Firefox.
Facebook now loads without issue!
Since I'm on a OSX 10.12 (Sierra) laptop, here's how to apply the Geekvisit guide on a Mac. This should go without saying, but be very very careful when you're in terminal. One careless mistake can really hurt your system. Follow my steps at your own risk. I will not be held responsible.
#1 Run terminal with Admin rights and execute the following commands:
MBP:~ jon$ cd "/Applications/Net Nanny/Net Nanny.app"
MBP:Net Nanny.app jon$ ls
ContentWatch Trusted Root Authority.pem Contents
MBP:Net Nanny.app jon$ cp "ContentWatch Trusted Root Authority.pem" ~/Desktop
MBP:Net Nanny.app jon$
#2 Navigate to Preferences->Privacy & Security
#3 Scroll all the way down to Certificates
#4 Click View Certificates
#5 Click on the Authorities tab, found along the top of the Certificate Manager
#6 Click on the Import button, found along the bottom of the Certificate Manager
#7 Navigate to where you just copied the PEM files (in my example it's the Desktop)
#8 Select the PEM file and click Open
#9 Click OK, found alogn the bottom of the Certificate Manager
#10 Restart firefox and then you are done!
Glad you're sorted
If you look up through the comments, you'll see someone else found that same article on geekvisit.com.
This is the more common certificate problem with NetNanny, where it doesn't import NetNanny's root certificate into the browser's certificate store.
The problem I hit is one that can happen even when that part is working correctly: On some sites, NetNanny uses a weak form of encryption for the step between NetNanny and the browser, making Firefox or Chrome mark the site as insecure even though the site itself is secured.
Enjoy NetNanny, and I hope you never hit this more complex problem.
I did acknowledge the other
I did acknowledge the other commenter who found that geekvisit article. First sentence of my post.
Anyway, I did wind up running into the SHA1 problem when attempting to uninstall a chrome extension. I'd be curious as to the exact sites you visited that cause this problem.
The other parental control tool to try would be Qstudio. Never tried it myself but heard that for content filtering it doesnt do as well, but it is better overall for monitoring and controlling your kids access to the net.
I did acknowledge the other
I did acknowledge the other commenter
So you did. :-) (Sorry I missed that!)
I'd be curious as to the exact sites you visited that cause this problem.
I found a really simple website where the main site itself tripped over on SHA1, and it was a site with basic games for kids that were purely educational (basic sums and so on, not a general flash games repackage site). I can't find that support ticket with NetNanny now to find it. But the one that failed on CSS / JS was Animal Jam - they use an Akimai CDN for their CSS, and it always needed manually allowing in the browser.
The other parental control tool to try would be Qstudio
Thank you. I think you mean this one. I hadn't met that one before, so it's great to have an alternative to look into.
Only some sites
Indeed that's a very good question.
I suspect it relates to something else that I don't understand: Why does it only bundle up the encrypted traffic using SHA1 for certain sites? It's obviously closed source, otherwise I'd have poked about by now and gone "aha - so that's why they're struggilng". I suspect that if I knew why some sites have to use a different cipher, I'd also see why it's not an easy fix.
I just tested the Animal Jam
I just tested the Animal Jam for you (https://www.animaljam.com/welcome). I tested loading the main page.
FF loaded it just fine.
Chrome did load it without any error messages but the page looks jacked, presumably because some CSS et al couldn't load.
BROWSER VERSIONS:
Firefox 60.0.2 (64-bit)
Chrome 70.0.3538.77 (64-bit)
A very well written explanation of SSL
I've been working on PCs since 1996 and doing Desktop Support / Helpdesk since 2005. I've always had a basic understanding of SSL and what it's for. But this gave me more in-depth knowledge.
I am indeed amazed that NN would fail to use SHA256 100% of the time.
It's now been 9 months since you wrote your article. Have you seen NN use SHA256 with more sites?
My Subscription expired
I've not used it at all. I told them that they had 3 months until my subscription ran out. I wasn't going to use it in the meanwhile, as it made the 'web unusable. After a while, I got an automated message telling me my subscription would expire in X weeks, so renew now to avoid loss of service. I replied and sent them the ticket number. After that, I never got any more automated reminders, not even an email when the subscription lapsed!
I could install on a test machine and test it - but you've just helpfully done that with Animal Jam for me, and I wouldn't put it on a machine in daily use.
Killed by Proxy-Analyzing Client-end TLS Interception Software
Dunno if it mentions NN, but thought you'd be interested. Published in 2017.
Alternatives mentioned in a technical paper
Strategic Cyber Security (2011)
There are many content filtering software products to choose from, including 8e6, CensorNet, Content Keeper, Cyber Patrol, Cyber Sentinel, DansGuardian, Fortinet, Internet Sheriff, K9, N2H2, Naomi, Net Nanny, SmartFilter, squidGuard, Surf Control, We-Blocker, Websense, and more. Each can be configured for a single schoolroom or an entire nation-state.
Good Find - Brilliant Paper
Thank you. Some of that is too technical for me to follow, but I follow most of it.
With regards to the specific problem we're discussing here, near the bottom of page 10 is this pair of sentences:
Regarding the hashing algorithm used for the certificate signature, 7 proxies replace the original certificate’s signing algorithm with SHA1, triggering security warnings in Chrome when the certificate expiration date is past December 31, 2015.
Does that remind you of anything?
There are other security weakneses which I had long wondered if NetNanny was prone to (wondering if it checks various problems upstream and then report them to the browser correctly). There are others I hadn't even thought of. And NetNanny is no worse in all this than the other products they test, differing only in exactly which situations of reduced security it leaves the end-user prone to.
Overall, this paper is pretty devestating. Many common anti-virus products, whilst they may make a computer more safe from viruses, make your web browsing significantly less safe.
This is in fact what they conclude (page 14):
While these applications may require TLS interception capabilities for their functionality, they must avoid introducing new weaknesses into the already fragile browser/SSL ecosystem. However, we found that not a single TLS proxy implementation is secure with respect to all of our tests, sometimes leading to trivial server impersonation under an active man-in-the-middle attack, as soon as the product is installed on a system. Our analysis calls the purpose of such proxies into question, especially in the case of antiviruses, which are tasked to enhance host security
Finally, our findings also call into question the so-called security bestpractice of using antiviruses on client systems, as commonly advised by IT professionals, and even required by some online banking websites.
As regards NetNanny's security generally, Appendix D reports the reponse they got when they raised these bugs with the software companies concerned. In general, they aim not to betray which companies responded with which levels of concern and commitment to address the flaws. But there is one section where it is possible to identify the company concerned:
One reply from a parental control software company highlighted several discrepancies and misconceptions. For example, our tests on the latest version of the product on Windows 7 SP1 with patches for Schannel against BEAST and FREAK reveal that it supports at most TLS 1.0 when connecting to remote websites. However, the company states that “In fact, Net Nanny supports …
You are awesome. The paper
You are awesome. The paper looked so dry and dense. You picked out the best bits, gave your own commentary and made me wanna read the whole paper.
It is sad when the very software that eliminates my porn use, makes my system less secure. Until I find something better than NN, I will need to stick with it.
Have you considered authoring some papers?
Yes. And no.
It is sad when the very software that eliminates my porn use, makes my system less secure. Until I find something better than NN, I will need to stick with it.
In that case, yes, it's important that you do. This can't become an excuse to turn off filtering.
Have you considered authoring some papers?
Not in this area, no. I used to work in IT as a programmer, but that was 15 years ago. I also have a lot of experience of the web hosting industry. But it remains a side interest.
Problem solved?
As I started using net nanny this week I had the same problems, thats how I got to this blog. I contacted them and was told, that this issue has been solved. I didn't yet try it, but that's what they sent me:
Please try the steps below in Firefox.
Click on Tools - Options - Advanced - Certificates and click in View Certificates. Under the Authorities Tab click on Import and change the File Type to All Files and browser to the following location and Import the file 'ContentWatch Trusted Root Authority.pem'
C:\Program Files\ContentWatch
Internet Explorer:
Click on Tools - Internet Options - Content and click on Certificates. Under the Trusted Root Certification and Import the file 'ContentWatch Trusted Root Authority.pem'
C:\Program Files\ContentWatch
Then restart both browsers and try again.
Chrome:
Open Chrome and access the Settings option in Chrome. Then click on Show Advanced Settings and click on Manage Certificates. Under Trusted Root Certification Authorities select Import and browse to the following location below and select the "ContentWatch Trusted Root Authority.pem" file. Be sure the file types are set to All files.
C:\Program Files\ContentWatch
Then restart the browser and try again.
Hope it will help.
Sadly not
They may have solved the problem, but if they have the steps you've just been given are not the solution.
You've been asked to do something that Net Nanny support seems to suggest as their first remedy for quite a few problems. There is an actual problem this solves. What you're doing is reinstalling Net Nanny's own root level certificate into your browser certificate store. (I mention the importance of this in the article). If, for some reason, your browser has lost this or never had it, then installing and trusting the certificate is important.
The problem I'm discussing is different, and this won't solve it. This is where the certificate is present and correct, but the Net Nanny proxy service re-encrypts SSL traffic using a weak cipher that the browser (correctly) refuses to trust because it's insecure.
If you look further up these comments, you'll see I replied to a comment from someone named Tord. His comment, and my reply, sums up why you haven't just been given the solution.
Make sure you test this thoroughly before your refund window closes. If you've just bought, you need to find out if it will be properly usable.
All the best!
Is NetNanny dead?
Just doing a little research because apparently NetNanny no longer blocks Microsoft Edge, period. Nothing is blocked. Since this is the core browser in Windows now, I'm not sure how they can continue to sell their product. Other browsers, and even IE 11 are blocked normally, just not Edge.
I opened a support case with them a while back and they said they were aware of the problem, but that was a while ago and no fix yet.
Seems there no choice but to move on to something better supported. Any suggestions?
NetNanny is quite good, but
NetNanny is quite good, but it costs 80$ bucks! We are using a FamilyFriendlyDNS.com for that matter, it's free and does it's job just as good.
Not sure I'd trust it
Thanks for the comment.
Did you actually read this post, or did you search for webpages with "NetNanny" where you could leave this comment. The article you're commenting on is actually about the fact that NetNanny is actually no good at all - until they fix a critical bug. So I'm intrigued you're opening line was conceding that "NetNanny is quite good".As for FamilyFriendlyDNS.com, I've done a little digging.
It's too long for a comment, so rather than put that here I've put up a fresh post detailing what I've found.
But what if you add, say, the
But what if you add, say, the website for Facebook Messenger to a list of allowed websites, would you then be able to access it, even though it is an https? I use NN for iPhone and I get this error: https://share.icloud.com/photos/034yQJpCpKhhfvmqZULjrAl6w
You'd still have the same
You'd still have the same problem, Matthew. You may be setting Messenger to be "allowed" by NetNanny, but the connection to Messenger still has to go through the NetNanny filtering system for it to work out that it's meant to allow that site. To do that, your computer has to connect through NetNanny's proxy service, so the problem I've documented (over 2 years ago now, but still not fixed) would get in your way.
I've had the same issue with Net Nanny, and your article helped me to realize that it was the problem! I use Covenant Eyes now (replaced it with Net Nanny, now I'm going back to it). I've never had issues with blocked SSL sites with Covenant eyes, but it can have issues manually blocking https sites (some, not all): it will block the site if it detects something objectionable, but not from the block list. To circumvent this, I block the unblocked sites using the 'hosts' file, then block the 'hosts' file folder using 'folder guard'. It's a complex combo, but it works. Covenant Eyes is the best of the best, despite the expense, and it seems able to adapt to the new internet.
Please email me is you have a question! I'm no expert, but I've got a system that works.